‘Ransomware’ is a type of malware that attempts to extort money from a computer user by infecting and taking control of the victim’s machine or the files or documents stored on it. • Typically, the ransomware will either ‘lock’ the computer to prevent normal usage, or encrypt the documents and files on it to prevent access to the saved data. Ransomware poses a threat to you and your device, but what makes this form of malware so special? The word “ransom” tells you everything you need to know about this pest. Ransomware is extortion software that can lock your computer and then demand a ransom for its release.
In most cases, ransomware infection occurs as follows. The malware first gains access to the device. Depending on the type of ransomware, either the entire operating system or individual files are encrypted. A ransom is then demanded from the victim. If you want to minimize the risk of a ransomware attack, you should rely on high-quality ransomware protection software.
Ransomware: part of the malware family
Malware is a portmanteau of the words “malicious” and “software”. The term malware, therefore, covers all malicious software that can be dangerous to your computer. This includes viruses and Trojans.
How do criminals install ransomware?
Ransomware generates a pop-up window, webpage, or email warning from what looks like an official authority. • Ransomware is usually installed when you open
- A malicious email attachment
- Click a malicious link in an email message
- an instant message on social networking site
- Ransomware can even be installed when you visit a malicious website.
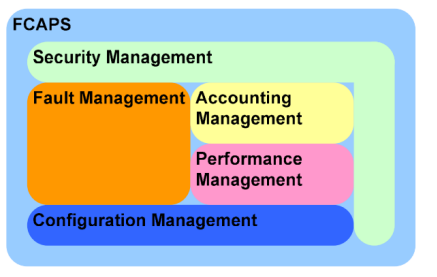
Types of Ransomware
- • Encryption Ransomware
- • Lock Screen Ransomware
- • Master Boot Record (MBR) Ransomware
Related link Kaspersky Security Lab