The website is the collection of web pages, different multimedia content such as text, images, and videos which can be accessed by the URL which you can see in the address bar of the browser. Static Website: In Static Websites, Web pages are returned by the server which are prebuilt source code files built using simple […]
Author: Code
How to Make a Simple Calculator in Java
Java is a programming language and computing platform first released by Sun Microsystems in 1995. There are lots of applications and websites that will not work unless you have Java installed, and more are created every day. Java is fast, secure, and reliable. From laptops to datacenters, game consoles to scientific supercomputers, cell phones to […]
Real world AI
One of the reasons why modern AI methods actually work in the real world – as opposed to most of the earlier good old-fashioned methods in the 1960-1980s – is the ability to deal with uncertainty. We use the following mathematical rules to implement Real-World Artificial Intelligence 1. Odds and probability. 2. The Bayes rule. […]
Electronic Transaction Act 2063
Legal provisions for authentication and regularization of the recognition, validity, integrity, and reliability of generation, production, processing, storage, communication, and transmission system of electronic records by making the transactions to be carried out by means of electronic data exchange or by any other means of electronic communications, reliable and secured. Objectives of the Electronic Transaction Act 2063 […]
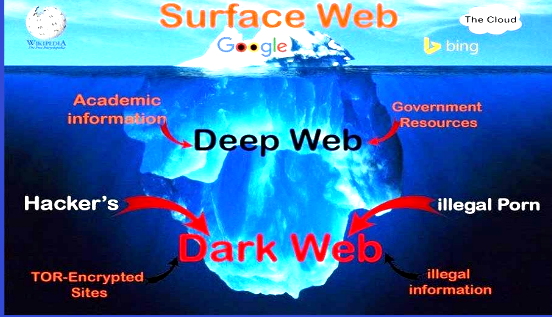
Dark Web and Deep Web
The creation of the world wide web and other search engines such as Google has made it easy to access information anytime. Most of this information is easily accessible on the surface web which is easily accessible through normal search engines. On the other hand, there are some websites that are not easy to access […]
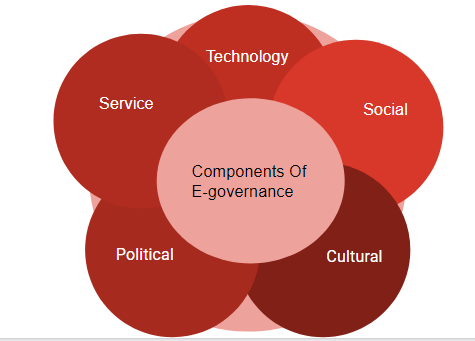
E-Government in Nepal
E-government is an idea raised by former U.S. vice president (Al Gore), within his vision of linking the citizen to the various agencies of government for getting all kinds of government services in an automated and automatic way, in addition to the completion of the government working itself depending on information and communication networks to […]
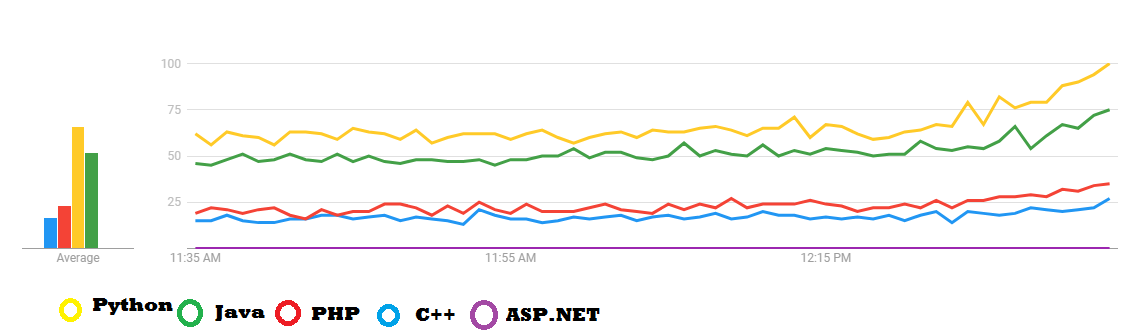
Top 5 Programming Language to Learn in 2020
A programming language is a standardized communication technique for designing and describing the instruction to the computer. Each programming language has a set of grammar and logic rules to define computer programs. The most important skill to learn in today’s world is to know how to write a computer program. Today’s business needs to search […]
How to use Laravel Encryption
Laravel Programming encrypter uses Open Secure Sockets Layer (SSL). It uses the AES-256 and AES-128 encryption Architecture for communication throw the client request and server response. encrypted values are signed using a message authentication code (MAC). Configuration You Must set a key option in your config/app.php configuration file You should use the php artisan key: […]
What’s New Coming to laravel V7.18
Laravel is a free open-source PHP programming framework developed by Taylor Otwell. It Packages Based on Symfony. Laravel Uses the MVC (Model, View, Controller ) Pattern on architectural design. The Latest Laravel released Version 7.18 With the improvement of an HTTP client middleware method and view component attribute updates, along with the latest new features, […]